Ariadezh unified threat management (UTM)
Ariadezh UTM
Ariadezh unified threat management (UTM)
Unified Threat Management (UTM) provides multiple security features and services in a single device or service on the network, protecting users from security threats in a simplified way. The advantage of UTM is streamlined installation and management of these multiple security capabilities. Ariadezh UTM filter network traffic to protect an organization from external threats. Maintaining features of stateful firewalls such as packet filtering, VPN support, network monitoring, and IP mapping features, Ariadezh also possesses deeper inspection capabilities that give them a superior ability to identify attacks, malware, and other threats.
Due to the vital and sensitive role of the firewalls of Dezhafzarnet Company, relying on the knowledge and technical experience of its security and programming team, it has designed and produced 100, 200, 300, 400, and 400 series firewalls.
The walls of Ariadezh Series 100, 200, 300, and 400 fireplaces are designed and produced in a completely indigenous way.
System features
Features of Ariadezh integrated threat management system
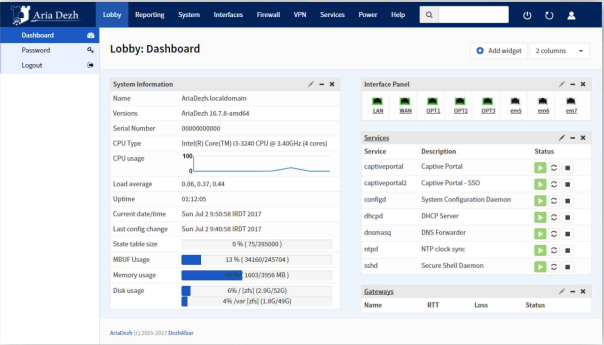
In the dashboard, you can have the latest system status in several columns with drag & drop capability. The dashboard environment is based on widgets, so that the users can add different widgets according to their needs, including:
- - High Availability
- - SSL Vpn
- - Dynamic DNS
- - Picture
- - Interface Statistics
- - Rss
- - IPsec
- - System Log
- - Load Balancer
- - Thermal Sensors
- - Firewall Logs
- - Traffic Graph
- - Network Time
- - Wake On Lan
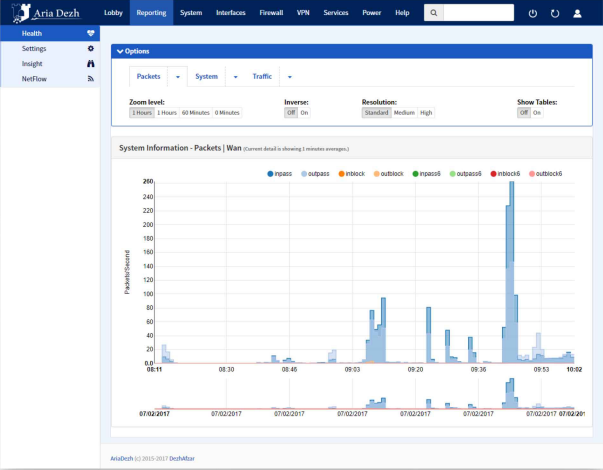
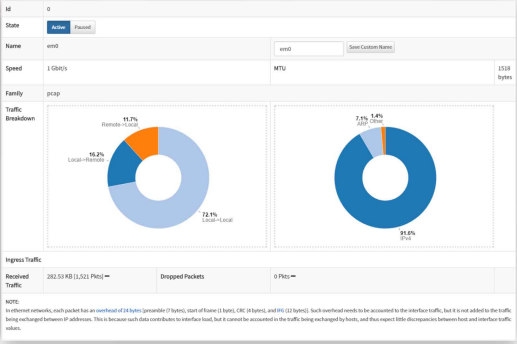
The reporting section provides the capability and monitor and reviews all events in the network and firewall.
- - Reporting the activity of different protocols: TCP, UDP, ICMP, IGMP
- - Reporting of passing traffic based on network interfaces
- - Reporting based on source and destination IPs separately
- - Full and detailed reporting of network interfaces characteristics and events
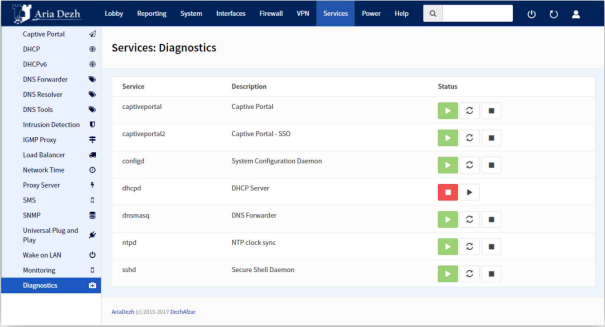
Ariadezh UTM provides a full range of diagnostics and troubleshooting tools, including :
- -ARP Table: Display the contents of the ARP table of the UTM
- - NDP Table: Network discovery protocol, similar to ARP tables for IPV6 protocol.
- - Packet Capture: Can be used to capture network packets passing through firewall interfaces, using various filtering rules
- - Test Port: This tool can be used to check if a service is up on the host system and is able to accept packets from a specific port. This tool uses the TCP protocol.
- - Traffic Graph: Diagram of traffic flow rate on different interfaces
- - Afinfo, Aftop, and AfTables: view the online status of the firewall, (e. g. interfaces statistics, connections statistics, etc.)
- - States Dump: Ariadezh is a stateful firewall and keeps states for tracking of all ongoing network connections. this allows the administrator to view firewall connection states.
- - States Reset: this can be used to delete connections and terminate ongoing connections.
- - States Summary: Display a summary of the current states.
- - Ping Traceroute: used for testing network connectivity
- - Filter Reload: To apply the rules in the firewall and observe possible errors in setting and applying the rules
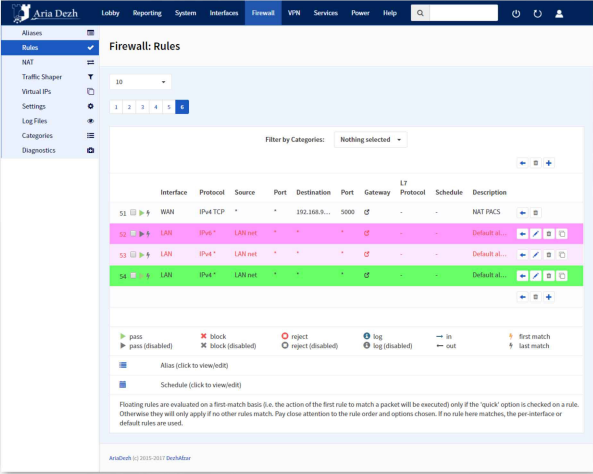
A firewall is a stateful firewall that maintains the path and state of network connections such as TCP streams and UDP communications. Ariadezh firewall allows users to categorize and manage rules. All the packets that intend to enter or leave the network may not be healthy packets and some of them may have a series of intentional or unintentional defects that cause harm to the host. The process of reconstructing packages and categorizing them is done by a feature called normalization.
The process of normalizing the packages is such that the final destination does not have any ambiguity in the interpretation of the packages. This feature also helps in defragmenting packets, discarding packets that have an invalid TCP flag (FLAG), and protecting the operating system against some firewall attacks.
- - Ability to categorize and color the rules
- - Ability to search in the rules
- - Ability to write rules based on the user's name
- - Ability to define timing for rules
- - The possibility of limiting the number of connections and nodes
- - SYN PROXY to counter SYN based attacks
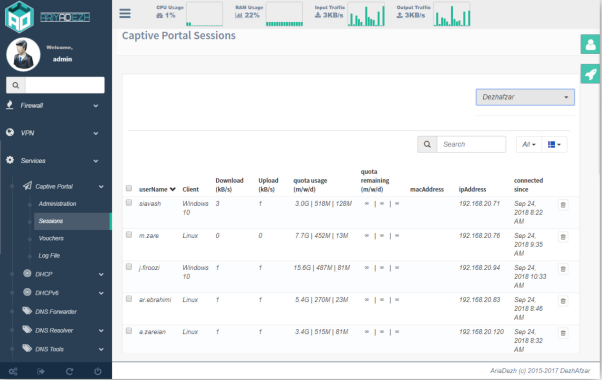
A captive portal allows you to force authentication on the network, or to redirect the user to another page that requires a click to access the network. This feature is usually used in hotspot networks, it is widely used in integrated networks to create an additional layer of security on the wireless network or the Internet. In addition, Ariadezh also supports vouchers. The voucher function generates random passwords that users can use to access the Internet through the captive portal and their access will be maintained until the voucher is validated. This feature is used in restaurants and hotels for users to access the Internet.
- - Support for the automatic single sign-on feature using the integrated windows authentication (IWA) protocol
- - Compatibility with all types of Windows servers
- - Support and compatibility with LDAP and radius
- - Detection and management of logged-off users
- - Display the status of connected users based on the amount of traffic consumed, current bandwidth, and operating system
the simplest and well-classified web interface of Ariadezh UTM, allows the network administrator to have complete monitoring of all parts of this product without complexity.
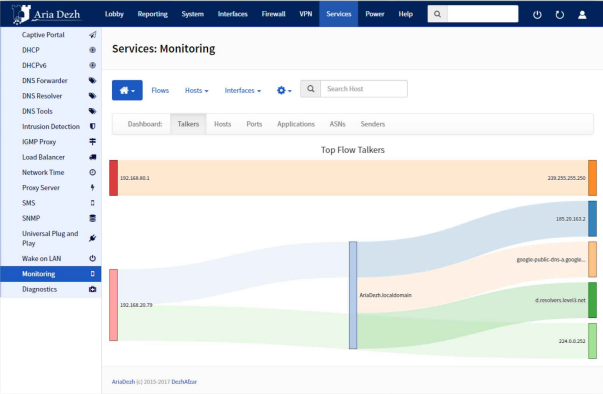
One of the unique capabilities of Ariadezh is the existence of a monitoring service that can analyze the network traffic in detail and present it to the administrator online. This service has the ability to display the traffic status in the following ways:
- - Arrangement of network traffic according to various network criteria such as throughput, protocols
- - Show network traffic, IPV4, IPV6
- - Generating comprehensive reports on various network metrics such as throughput, protocols
- - - Providing reports for each branch of network communication including RTT delay report, TCP statistics, and bytes/packet
- - Continuous storage of traffic statistics on disk in RRD format
- - Reports based on host geographic locations
- - Discover application protocols by investigating network traffic
- - Exploring TLS/SSL certificates in encrypted communications
- - reports on how TCP/IP traffic is spread among different protocols.
- - Display IP traffic distribution among different protocols
- - IP traffic analysis of the matrix subnet (specifying the two sides of the communication)
- - IP protocol usage report organized by protocol type
- - Generate HTML5 / AJAX network traffic statistics
User manual is essential for any product. Ariadezh user manual is fundamentally different from other similar products. This guide is completely practical and scenario based. In order to activate each service, a tested scenario has been presented step by step.

In Ariadezh, there is the ability to check layer 7 traffic via which we can identify application layer protocols and determine the type of traffic allowed to pass through, thereby ensuring that there is no possibility of passing traffic with undesirable protocols.
Types of recognizable protocols:
- - HTTP
- - FTP
- - IMAP
- - SMTP
- - SSL / TLS: For protocols such as HTTPS, IMAPS, SMTPS, FTPS, etc., which implicitly use the TLS protocol, the SSL / TLS option must be selected
- - SSH: SSH option must be selected for FISH, RSH, SCP, SFTP, SSH, and any protocol that uses SSH tunnel
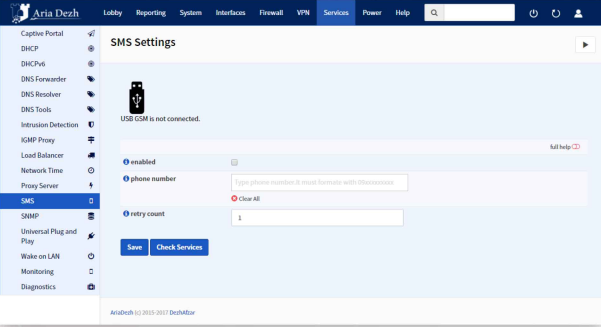
With the help of this feature, the major events of the firewall are sent via a GSM module to the defined phone numbers.
Ariadezh has a system hardware failure detection feature. So that two or more firewalls can be configured as a failover group. If a network interface on the primary firewall is down or the primary firewall is completely down, the secondary firewall is activated. The use of this powerful feature turns Ariadezh into a stable and non-failing firewall. During the automatic transition to the backup version, the network connection will remain active with minimal interruption for users.

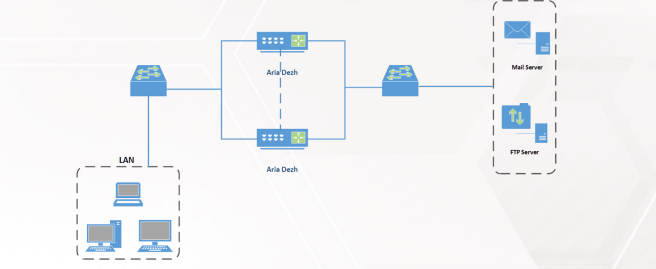
In order to balance and not impose an additional load on a server, the Load Balance technique is used. Using this feature, if one server is interrupted, the passing traffic will be spread to other servers. Therefore, using Load Balance will increase system reliability.
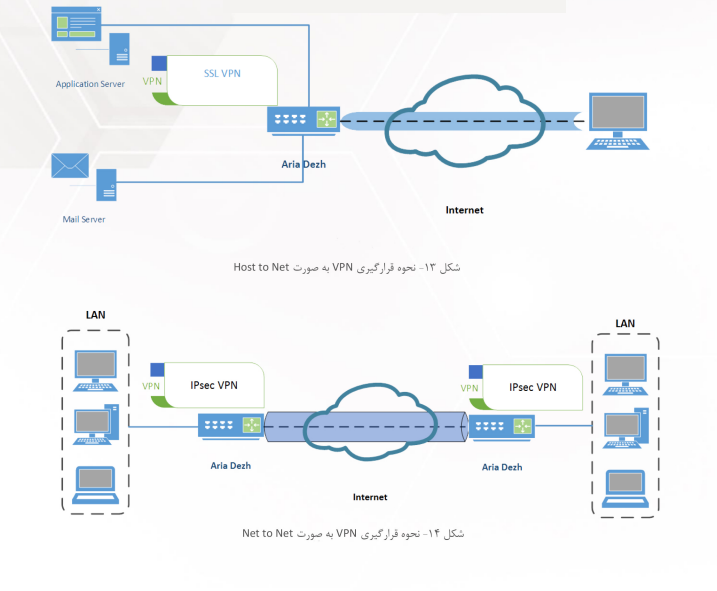
VPN stands for virtual private network, which literally means virtual private network. VPN is used to securely connect two networks or subnets.
IPsec is an abbreviation for IP Security, which refers to a series of protocols that support the secure exchange of packets in the IP layer.
IPsec is widely used in VPN technology for authentication, confidentiality, integrity, and key management in IP-based networks.
Ariadezh provides a wide range of VPN technologies, from today's SSL VPN to older technologies such as IPsec and L2TP. Site-to-Site and Roadwarriar settings can be done in minutes with the export feature of user settings.
- - Ability to apply and support customer order encryption algorithms.
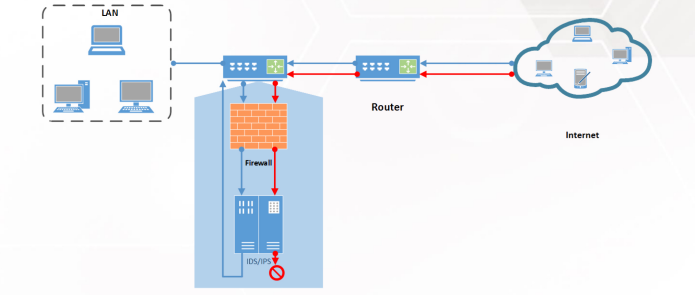
IDS and IPS technologies analyze network traffic in more detail than a firewall. Similar to antivirus systems, IDS and IPS tools analyze traffic and compare each packet with a database of known attack profiles. When attacks are detected, these tools kick in and notify authorities of an attack, tools go one step further and automatically block malicious traffic. The IPS component in Ariadezh defends the network in two steps:
By detecting abnormal behavior in the network, it prevents DDOS attacks and occasional scanning.
By using the pattern of attacks, it deals with attacks such as Backdoors and Exploits.
- - Ability to write complex rules by users
- - Ability to block HTTP and HTTPS sites
- - Ability to view logs with very fast filtering
- - Intelligent management of logs with very fast filtering
- - Using the ZFS file system to increase efficiency in storing and retrieving logs
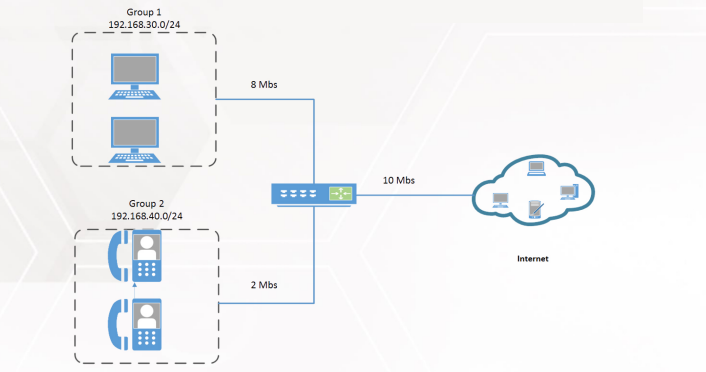
One of the required features in the network is a traffic sharing feature. This feature of traffic bandwidth is allowed to control the links. In fact, by using this feature, you give your data and traffic the maximum speed or you can apply restrictions on the traffic sent.
Traffic distribution in Ariadezh is very flexible and is organized around pipes, queues, and related rules. Pipes define virtual bandwidth, queues can be used to prioritize traffic within each pipe, and finally, rules are used to form a specific packet flow. Traffic sharing rules are independent of firewall rules and other settings.
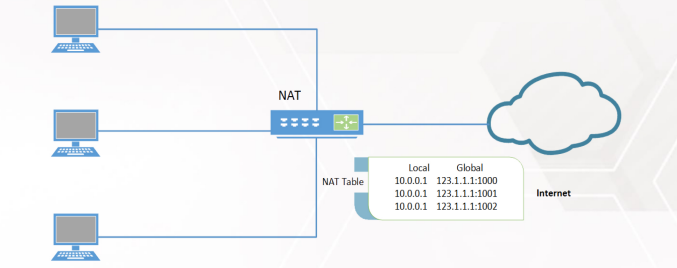
Full support for NAT feature:
- - Port Forwarding (Destination Nat): the ability to make a direct connection for a specific service on the side of the secure network on a host without a public IP address
- - Outbound Nat (Source NAT): Translates outgoing traffic based on the source IP
- - One-To-One: Translation of a specific address to another specific address
- - NPT (IPV6): Translation of an IPV6 address to another IPV6 address

Ariadezh product has different deployment statuses, including:
- - Bridge: If the Ariadezh firewall is launched in Bridge mode, it has the ability to act as a Transparent Bridge (Layer 2). In this case, the firewall can check layer 3 and higher. In this case, Ariadezh is placed between the internal network connection and the router and inspects the traffic without the need for changes in the network architecture.
- - NAT/Router: In this case, the firewall is deployed as a gateway or router between two networks. In most cases, it is placed between the secure network and the Internet, and in addition to the address translation function, it will also perform routing operations.
In order to prevent unauthorized access and possible misuse, Ariadezh product supports two levels of authentication. Network traffic authentication (Data Plane) and system user interface authentication. Authentication of network traffic allows the identification of the user sending the traffic so that the user is allowed to send the traffic if he/she has been authenticated before. User interface authentication is used to prevent unauthorized access to the management panel.
- - Support for users (Active Directory), RADIUS, LDAP, and users defined in the system
- - Identification of users who have permission to send traffic
- - Personalization of the authentication page template (Captive Portal)
- - Compatibility with all types of Windows servers
- - Display the list of users and manage them
- - Management and detection of inactive and logged-out users
- - Two Step Authentication in the management panel using password and SMS
- - The ability to disable HTTP, HTTPS ports and their automatic activation if the user establishes an SSH connection. With the help of this feature, the web user interface of the firewall is not exposed to attackers.
- - The possibility of SSH preauthentication to prevent access to the user interface until the first successful login in the SSH console
Support for different versions of SNMP protocol
- - Real-time monitoring of network connections
- - Consistency on the performance of users: the amount of bandwidth consumed, such as online status and...
- - Real-time information about the state of firewall performance, possible errors, and network and firewall events
You can use this service to control and monitor http, https, ftp traffic. The proxy provided by Ariadge has facilities such as batch web-filtering and access control. This service can run in transparent mode. With the combination of proxy, firewall and captive portal, you can have a very good monitoring of users and their actions, in such a way that users' access can be controlled by captive portal, and http and https traffic can be controlled by proxy. For example, it is possible to limit a user's access to a website or address. It is also possible to integrate this feature with antiviruses that have an ICAP interface.
- - Applied restriction rules to user's access
- - Record users events
- - Record users web-traffic
Static routing: With this feature, the network administrator can define routing based on the destination IP.
Policy-based routing: In this method, routing can be defined based on other components of an IP packet, such as source IP, source port, and destination. This feature enables routing with the help of firewall rules. Each firewall rule allows the selection of a gateway port, and if no port is selected, the flow passes through the default port or according to the routing table.
Dynamic routing: Here, various dynamic routing protocols such as OSPF, BGP, and RIP can be configured and used.
In this section, there are elements of allocation, adjustment, and control of network interfaces. Types of network interfaces:
- - Bridge: the second layer of the bridge in order to connect two or more interfaces to each other in the mode (broadcast/collision domain)
- - GIF: IPV6 and IPV4 create a logical tunnel for traffic
- - GRE: to create a point-to-point connection (tunnel) between hosts
- - Group: to categorize a group of interfaces and apply rules to them in order to avoid rewriting the rules
- - LAGG: the possibility of combining several interfaces and converting them as a virtual interface in order to increase the speed of links and increase fault tolerance
- - VLAN: the creation of a virtual local network
Since the secure storage of sensitive data such as cryptographic keys is a serious challenge. The presence of native Ariaki tokens associated with Ariadezh can satisfy many security concerns with the presence of foreign hardware. Also, in addition to secure data storage, this token has the possibility of symmetric encryption.
With this feature, the probability of the firewall and servers in the network being interrupted is as low as possible.
Full support for DHCP service in the following situations:
- - DHCP Server: automatic assignment of IP addresses to network hosts
- - DHCP Relay: to send and receive DHCP requests between hosts and servers that are not in the same subnet (broadcast domains)
- - DHCPV6 Server and Relay: Automatic allocation of IPv6 addresses to network hosts. The Relay function is the same as IPv4, except that it is used for IPv6.
- - The ability to display the IPs assigned by the server to the users along with the complete information of the users
- - Ability to report the DHCP service
- - Support for DHCP Static Mapping service: to assign static IP addresses to desired hosts.
Here, it is possible to block these websites through IPS. The difference between this blocking and the use of web proxy is that the blocking is done at gigabyte speed and without decoding HTTPS traffic.
- - DNS Forwarder: a feature to send DNS requests (queries) to DNS servers outside the internal network
- - DNS Resolver: a feature to answer host queries and convert the domain name to IP
- - DNS Tools: a set of tools for better control and use of DNS such as DNS Lookup, Dynamic DNS, and DNS Filter
- - DNS Crypt: a feature to maintain the confidentiality of DNS traffic
In this section, we can define and manage different users and groups.
- - Assigning users to different and identical groups
- - Time management of users' meetings
- - Definition of different servers: LDAP, Radius, Voucher, and...
- - Ability to define a mobile number to send SMS
- - Ability to define daily, weekly, and monthly traffic volumes
- - Ability to manage access to different parts of Ariadezh
The possibility of using and adding a list of IP addresses based on their geographical location. This allows traffic to be blocked or passed based on the country of origin or destination of the traffic. This database is constantly being updated.
Managing firewall rules is not an easy task. Using aliases you can list various IPs, hosts, networks, or port numbers in a group for use in firewall rules. Aliases are the definition section of the external firewall.
Here you can control and monitor the traffic volume and bandwidth consumption of users.
- - Ability to define consumption volume based on day, week, and month for users or groups of users
- - The ability to view the consumed volume and the remaining volume of users
- - Display the amount of traffic consumed by each user
Ariadezh can act as a gateway or proxy for H.323 protocol. This feature allows more control over VOIP traffic in the network. It can also solve the issues and problems that H. 323 and SIP have in public firewalls.
Dezhafzarnet Company (Dezhafzar) has prepared a video and catalog to improve product introduction and provide better interaction with customers. By using the buttons below, you can get to know more about this native product.
other products